Cyber resilience is no longer about whether an organization can prevent an attack—it is about whether the business can continue to operate, recover trust, and protect value when prevention inevitably fails. Ransomware, destructive malware, insider threats, and supply‑chain compromises have made data recovery a board‑level risk with direct financial, legal, and reputational consequences. A “perfect” cyber‑resilient architecture does not mean eliminating all risk; it means designing systems that assume compromise, limit blast radius, preserve recoverability, and restore critical operations with confidence. The architecture outlined below represents what resilience looks like when it is treated as a business continuity mandate, not just an IT control.
1. Core Principles of a Perfect Cyber‑Resilient Architecture
A truly resilient design must deliver:
- Continuity — operations continue even during an attack
- Integrity — backups cannot be altered, encrypted, or deleted
- Recoverability — rapid, orchestrated restoration to a known‑good state
- Visibility — ability to detect malicious activity early
- Adaptability — lessons learned feed back into the system
- Containment — The architecture must prevent compromise from spreading across environments, including backup and recovery planes
These align with modern cyber resilience frameworks.
2. The Architecture: What “Perfect” Looks Like
A. Multi‑Layered Backup Architecture
1. Production Layer (Primary Systems)
- Hardened OS and applications
- MFA everywhere
- Network segmentation
- Least‑privilege access
- Continuous patching and vulnerability management
- Endpoint protection + EDR/XDR
- Identity Protection
- Supply chain/third-party risk (compromised software updates are a leading ransomware vector)
- Secrets management (hardcoded credentials in scripts routinely expose backup systems)
2. Backup Layer (Operational Backups)
- Immutable storage (WORM, object lock, or filesystem immutability)
- Separation of duties (backup admins ≠ domain admins)
- MFA + RBAC for backup platform
- Encrypted in flight and at rest
- Frequent backups aligned to RPO
- Automated backup verification
- Backup infrastructure isolation
- Hardening the backup server OS
- Restricting inbound connections to the backup servers
- Monitoring the backup service account
3. Isolated Recovery Layer (Cyber Recovery Vault)
- Physically or logically isolated from production
- Strictly controlled access (just‑in‑time, MFA, break‑glass)
- Immutable, air‑gapped or logically gapped copies
- Malware scanning on ingest and before restore
- Golden images / golden configs stored here
- No direct domain trust with production
This layer is critical for ransomware resilience.
3. Security Controls That Must Wrap the Backup Ecosystem
A. Protect the Backups Themselves
- Immutable snapshots
- Air‑gap or logical gap
- One-way replication/data diode – enforces hardware-level unidirectional flow, so a compromised production network cannot reach back to the vault
- MFA for all privileged operations
- RBAC with least privilege
- No shared service accounts
- API rate limiting and anomaly detection
- Backup infrastructure hardened and isolated
B. Detect Malicious Activity
- File‑system anomaly detection (encryption, mass deletion)
- Backup size deviation alerting — a sudden 40% increase or decrease in backup job size is one of the earliest detectable signals of encryption or mass deletion activity.
- Behavioral ransomware detection
- Threat hunting using historical telemetry
- SIEM/XDR integration for backup events
- Alerts on unusual backup deletions or policy changes
- Backup deletion delay/approval workflows
- 24–72 hour deletion delay
- Multi-Party Approval
These align with modern ransomware detection guidance.
4. Incident Response & Recovery Readiness
A. Response Playbooks
- Documented ransomware response plan
- Out‑of‑band communication channels
- Pre‑defined roles and responsibilities
- Legal, PR, IR, and executive alignment
B. Recovery Playbooks
- Pre‑built orchestration workflows
- Golden master images for critical systems
- Clean‑room recovery environment
- No outbound internet
- No inbound connections
- No trust relationships
- Temporary identity provider
- Forensic tooling
- Malware scanning before restore
- Prioritized application tiers (Tier 0 → Tier 3)
- Ability to restore AD, DNS, and identity systems first
C. Testing
| Test Type | Freq | Recommended Freq |
|---|---|---|
| Tabletop | Semi-Annually | Quarterly |
| Partial restore tests | Quarterly | Monthly |
| Backup validation | Automated | Continuous |
| Full recovery simulation | Annually | Annually* |
*Annual is acceptable for full failover if partial restores are monthly and tabletops are quarterly.
Testing is a core pillar of cyber resilience.
5. Governance, Risk, and Business Alignment
A. Risk‑Driven Design
- Map critical business processes
- Define RPO/RTO by business impact
- Align cyber insurance requirements
- Insurers increasingly require documented evidence of immutable backups, MFA, and tested recovery
- Maintain updated risk assessments and audits
- Data Classification – Not all data needs the same RPO/RTO or the same vault tier.
- Tier recovery objectives by data sensitivity and business criticality; this is foundational to a cost-effective design
B. Executive & Cross‑Functional Engagement
- Cyber resilience is not an IT‑only function
- Requires business, legal, compliance, and operations
- Maintain a cross‑functional ransomware resilience team
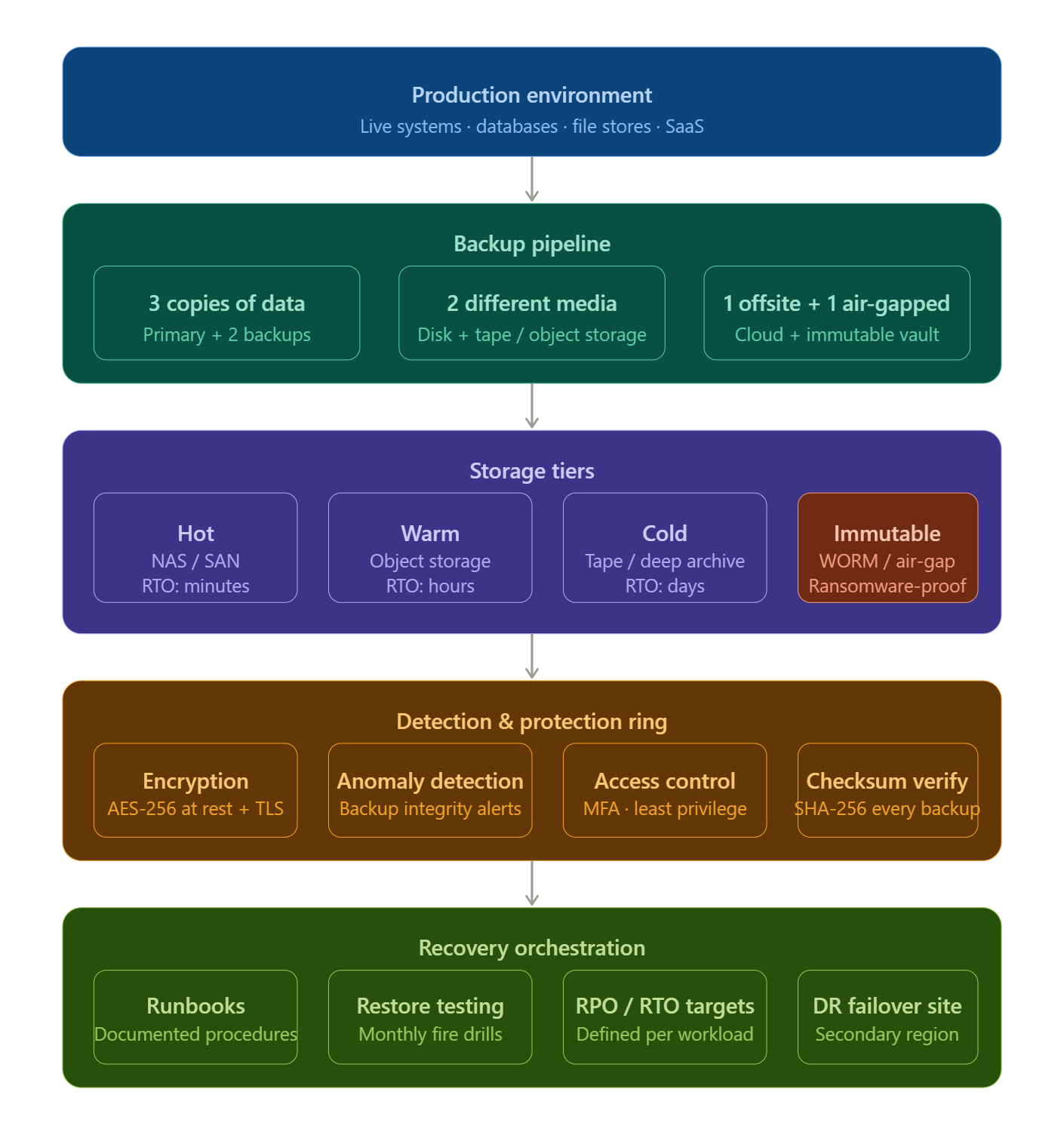
6. What “Perfect” Looks Like in One Diagram
Three‑Tier Cyber‑Resilient Backup Architecture
The diagram below illustrates strict control-plane separation: production can write forward, but cannot authenticate, enumerate, or traverse backward into the recovery vault
The “Perfect Setup” Checklist
Identity & Access
- MFA everywhere
- No shared accounts
- Backup admins are isolated from the domain admins
Backup Platform
- Immutable storage
- Air‑gap or logical gap
- Automated verification
- Anomaly detection
- Encrypted everywhere
Recovery
- Clean‑room environment
- Golden images
- Malware scanning pre‑restore
- Orchestrated recovery workflows
Governance
- Documented IR/DR playbooks
- Quarterly tabletop exercises
- Annual full recovery tests
- Continuous improvement loop
Closing Thoughts
A truly cyber‑resilient organization is defined not by the tools it deploys, but by the discipline of its design, the rigor of its testing, and the clarity of its governance. Perfect resilience is not achieved in a single project—it is built through layered architecture, continuous validation, and cross‑functional ownership that aligns technology, risk, and business priorities. Organizations that invest in immutable backups, isolated recovery environments, and practiced recovery workflows are not merely improving IT outcomes; they are protecting revenue, customer trust, and enterprise survival. In an era where cyber incidents are inevitable, resilience is no longer optional—it is a core competency of modern leadership.