1. Core Principles
A modern, cyber‑resilient DR architecture must deliver:
- Zero‑trust security across identities, endpoints, networks, data, and workloads.
- Resilience against ransomware and destructive attacks (including AI‑assisted attacks).
- Rapid, automated recovery to minimize downtime.
- Immutable, independently stored backups across multiple zones/clouds.
- Automated testing to prove recoverability.
- AI‑powered anomaly detection, prediction, and orchestration.
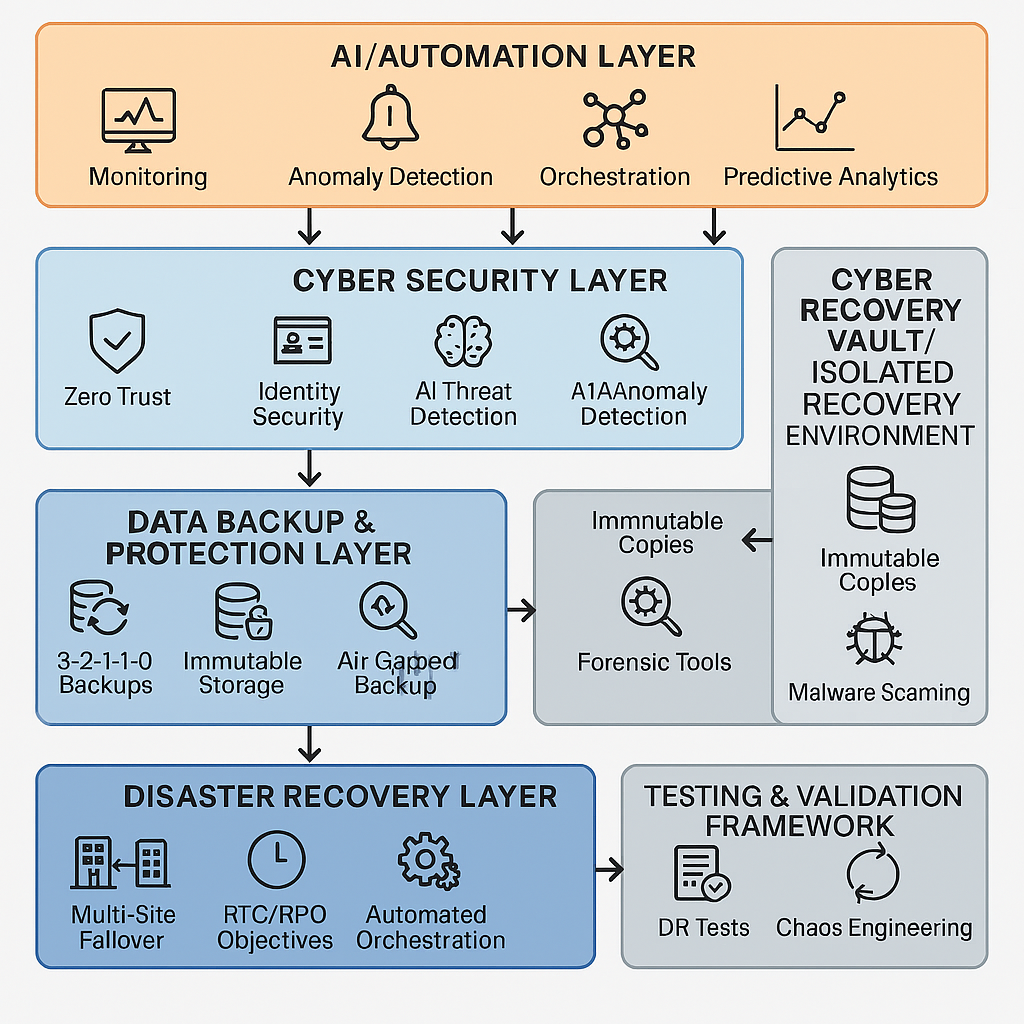
A. Cyber Security Layer
Objective: Prevent, detect, and contain cyber threats before they compromise data.
Best Practices
- Zero Trust Framework
- Identity-based access controls (MFA, conditional access).
- Network micro‑segmentation.
- Least privilege for admins.
- Verify explicitly.
Continuously authenticate and authorize based on all available data points,
including user identity, location, device health, service or workload, data
classification, and anomalies. - Use least-privileged access.
Limit user access with just-in-time, and just-enough-access (JIT/JEA), risk-based
adaptive policies, and data protection to help secure both data and productivity. - Assume a breach.
Rather than acting as though the attack is coming, Zero Trust treats any
situation as though the breach has already occurred. This not only improves
prevention, but in the case of a breach, it can minimize its impact and help
prevent cross-system access and further damage
- Verify explicitly.
- Endpoint + Server Hardening
- EDR/XDR solutions with behavioral detection.
- Endpoint Detection and Response
- Extended Detection and Response
- Privileged Access Workstation (PAW) model for admins.
- EDR/XDR solutions with behavioral detection.
- AI‑Driven Threat Detection
- ML-based anomaly detection, e.g., sudden encryption activity.
- AI‑powered behavioral baselines for users, devices, and applications.
- Security Controls
- Continuous vulnerability scanning.
- Automated patching.
- Application allowlisting.
- Secure configurations and baselines.
B. Data Protection & Backup Layer
Objective: Ensure reliable, protected, manipulatable‑proof data copies.
Best Practices
- 3‑2‑1‑1‑0 Backup Standard
- 3 copies of data
- 2 media types
- 1 copy offsite
- 1 immutable or air‑gapped
- 0 errors verified via automated testing
- Backup Tiers
- Primary Hot Backup
- A Primary Hot Backup is the fastest, most recovery‑ready form of data protection. It provides real‑time—or near‑real‑time—protection of production systems by continuously replicating block‑level or journaled changes to a secondary system.
- Continuous replication or near-CDP.
- Continuous Replication captures every write made on the primary system and instantly sends it to a secondary storage target with extremely low latency. There is no backup window—protection happens 24×7.
- Near‑CDP replicates data at very short, frequent intervals (e.g., every 15 seconds, 30 seconds, 1 minute). It emulates CDP while reducing the infrastructure stress of true continuous write replication.
- Fast RTO.
- Not Ideal For
- Cold/archive data
- Low‑risk workloads
- Systems with intermittent connectivity
- Secondary Backup (Immutable)
- WORM storage, object‑lock, or virtual air‑gap.
- Tertiary Offline Copy
- Tape, vault, or cloud deep-archive.
- Continuous replication or near-CDP.
- A Primary Hot Backup is the fastest, most recovery‑ready form of data protection. It provides real‑time—or near‑real‑time—protection of production systems by continuously replicating block‑level or journaled changes to a secondary system.
- Primary Hot Backup
- Backup Security
- Isolated backup network.
- Backup admin identities are separate from production identities.
- Immutable snapshots (cannot be deleted, even by admin).
- AI Integration
- Detect anomalous backup patterns (e.g., sudden spike in changed blocks).
- Predict backup failures before they happen.
- Recommend optimal backup schedules based on usage patterns.
C. Disaster Recovery (DR) Layer
Objective: Maintain business continuity after failures or attacks.
Best Practices
- Define Recovery Objectives
- RPO (Recovery Point Objective)
- RTO (Recovery Time Objective)
- Multi‑Site DR
- Active/active or active/standby, depending on application criticality.
- DR should be in a separate region, cloud, or data center.
- Automated DR Orchestration
- Runbooks codified as automation workflows.
- Test failovers without impacting production.
- AI Integration
- Predict DR capacity needs.
- Recommend failover paths.
- Autonomous failover using policy‑based ML decisions.
D. Cyber Recovery Vault (Isolated Recovery Environment – IRE)
Objective: Provide a last‑resort clean environment immune from attacks.
Key Vault Features
- Physically or logically isolated network.
- Multifactor administrative access with strict just‑in‑time elevation.
- Immutable copies are replicated on schedule but not continuously (prevents malware spread).
- DR Tools Inside the Vault
- Malware scanning.
- Forensic analysis.
- Zero-trust access controls.
- AI Integration
- AI‑driven malware scoring and clean-room validation.
- AI-based anomaly detection on restored data.
3. AI‑Driven Enhancements Across the Stack
AI Use Cases
- Threat Detection & Prevention
- Behavioral analytics (UEBA/UEAI).
- Real-time ransomware signature detection.
- Backup & Recovery Optimization
- Predict failures in backup chains.
- Identify unusual encryption or deletions.
- DR Recommendations
- Predict which systems need the fastest RTO.
- Automated Incident Response
- ChatOps + AI‑assisted triage.
- Suggest isolation or failover actions.
- Testing Automation
- Generate and evaluate DR test scenarios.
- Compare test outcomes to historical performance.
4. Testing & Validation Framework
A resilient system must prove it works.
A. Backup Testing
- Automated restore verification (checksum validation).
- Randomized restore tests weekly.
- Full restore simulation monthly.
B. DR Testing
- Quarterly failover tests.
- Annual full DR simulation (all systems).
- AI‑randomized “chaos” tests:
- Simulate a ransomware attack
- Simulate file corruption
- Simulate region failure
- Evaluate the time to detect and the time to restore
C. Cyber Resilience Testing
- Incident response tabletop exercises.
- Cyber‑range simulations.
- Penetration testing of:
- Backup systems
- DR orchestration tools
- Vault access procedures
D. AI Validation
- Validate that AI did not produce false positives during failover tests.
- Monitor ML models for consistency and drift.
5. End‑to‑End Blueprint (High Level)
- Secure the environment
- Zero trust, segmented networks, strong identity protection.
- Protect the data
- 3‑2‑1‑1‑0 backups with immutability.
- Deploy the Cyber Recovery Vault
- Isolated restoration environment.
- Enable AI Analytics
- Threat detection + anomaly monitoring + automated recovery.
- Automate DR runbooks
- Policy-driven, testable, monitored workflows.
- Implement rigorous testing
- Backup tests, DR simulations, cyber-range exercises.
- Continuous improvement
- Lessons learned from tests and incidents feed back into the architecture.